Shift-left data quality: Why downstream checks are too late for data products and AI
Part 1 of 3 in our “Shift-Left Data Trust” series.
You get an alert. A data quality threshold was breached for a critical asset.
Or an AI workflow that’s being used in production starts returning results that are wrong.
The impending dread hits you, and you start asking yourself: Why did we catch this so late? Where did it break? How far did it spread? What else is affected?
That is the real problem shift-left is meant to solve.
Because in most organizations, the problem is not that issues are impossible to detect. It’s that they’re detected after they’ve already moved through pipelines, reached downstream systems, and expanded their blast radius.
So the scramble begins. Teams trace lineage. They inspect jobs, dependencies, and handoffs. They try to find the point where the issue first entered the flow and fix it upstream, in a pipeline or source system that was never properly covered in the first place.
That’s data downtime. And it’s expensive, with various research analysts estimating average annual losses between $5M and $12.9M due to data quality failures.
AI makes the impact sharper. In RAG-based and agentic architectures, data doesn’t just inform people. It informs systems that act. When low-quality data is embedded into a knowledge base or used to trigger automated decisions, errors don’t just show up as a wrong chart. They can affect pricing, credit decisions, customer communications, shipment routing, or compliance outcomes.
That’s why “data quality at the end” is no longer enough. Not because it never catches issues, but because it catches them at the wrong end of the cost-to-fix curve.
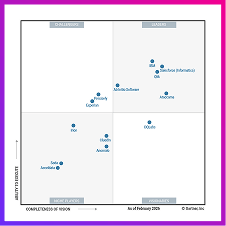
The market is shifting toward a new expectation: Move data quality, governance, and validation upstream, closer to where data is created and transformed. In other words: shift data trust left.
What “shift-left” means in data management (and why it’s different from “add more tests”)
In software, DevOps and DevSecOps moved testing and security earlier in the lifecycle: automated tests in CI, security checks on every commit, and guardrails built into the developer workflow.
In data management, it’s the same idea, but the “product” is the data itself.
Shift-left data management means enforcing expectations earlier, before bad data propagates across pipelines, dashboards, and AI systems. It’s a lifecycle approach that combines:
- Data quality (is the data correct, complete, timely, and consistent?)
- Governance (who owns it, what it means, what’s allowed?)
- Operational controls (what happens automatically when something breaks?)
It’s easy to oversimplify shift-left as “add more tests.” So here is the key distinction: Shift-left isn’t “more monitoring” or “more checks.” It’s moving validation upstream and making it enforceable as part of the way data is produced and collected. In order to build data products, you need clear ownership, standards, and continuous feedback.
The cost-to-fix curve is real, especially in modern stacks
Even with cloud-scale platforms, the economics haven’t changed. They’ve intensified.
When quality issues are caught late (after transformation and consumption), the cost multiplies. It’s not just the bug; it’s the downstream compute, re-runs, cross-team coordination, and the time spent proving what went wrong. The classic 1–10–100 rule still applies, and it’s a simple way to remember this cost curve:
- Catch an issue at the source (bad payload rejected, invalid reference value blocked). The fix is small and costs “$1.”
- Catch it mid-pipeline, and you’ve already paid roughly 10x for compute, orchestration, and partial propagation.
- Let it reach reports, AI models, or regulatory outputs, and the cost can balloon to 100x once you factor in remediation, lost trust, and potential fines.
If your organization is spending a meaningful percentage of engineering time tracing data downtime across tools, you’re living this curve.
Why shift-left matters now
Shift-left is not a trendy rebrand of data testing. It’s a response to three converging forces that are challenging the classic way how data teams operate.
1) AI removes the “human safety net”
Traditional workflows have a built-in pause: humans review outputs. When something looks off, an analyst asks questions.
Agentic systems and RAG pipelines don’t stop to ask if your input data is trustworthy. They read data and act: update records, send messages, reroute operations. If the knowledge base feeding your LLM is duplicated, inconsistent, or stale, the model will hallucinate with high confidence. The implication is simple:
Validation must occur before vectorization, preventing bad data from becoming “truth.”
2) Federated architectures & data mesh
Your landscape is probably a mix of microservices, domains, and cloud platforms. Teams own their own schemas, release cycles, and pipelines. Central data teams can’t babysit every schema change or new feed.
Data mesh principles define “data as a product” with domain ownership and SLAs. In practice, this only works if producers can enforce contracts and quality at the edges, and if those rules are reusable and visible across the enterprise. So trust has to be built into how data products are produced.
3) Risk and compliance demand traceability
In regulated industries, “We found it later and fixed it” is not a satisfying answer. Due to regulations like GDPR, CCPA, and the EU AI Act, data quality and lineage are now treated as compliance requirements, especially for high‑risk AI systems. You need to be able to prove:
- Clear ownership and definitions
- Evidence of controls and monitoring
- Traceability from source to consumption
- Documented remediation paths
And that’s impossible if your controls exist only as SQL in a warehouse job or as tribal knowledge within a single team. Shift-left helps turn data quality from an after-the-fact cleanup exercise into a repeatable control system.
A simple mental model: Put trust boundaries inside your data lifecycle
The easiest way to make shift-left practical is to stop thinking about “one big data quality program” and start thinking about trust boundaries as places where quality and policy are enforced before data moves forward.
Most organizations need three.
Trust boundary 1: Data capture and ingestion
This is where data is born: APIs, operational applications, event streams, source extracts.
Shift-left here means:
- Validating schemas and required fields
- Enforcing reference values (codes, categories, statuses)
- Rejecting or quarantining invalid records early, with clear feedback to producers
This is where you prevent bad data from becoming “normal.”
Trust boundary 2: Pipelines and transformations
This is where teams feel the pain. ELT/ETL jobs, dbt models, orchestration runs, and lakehouse transforms. Here, shift-left means you:
- Treat transformations like software builds: checks must pass before the pipeline is considered “healthy”
- Run data quality checks at the right points (before/after major transformations, before publishing curated outputs)
- Use consistent rule definitions, so data quality doesn’t depend on who wrote the SQL
- Add proactive pipeline monitoring and alerting, so you catch failures, delays, schema drift, and unexpected volume shifts before they reach dashboards, data products, or AI workflows
- Route alerts with clear ownership and follow-through, so incidents don’t disappear into chat threads or inboxes
This turns pipelines into enforcement points, not just conveyor belts.
Trust boundary 3: Storage and consumption
Data lands in warehouses, lakehouses, semantic layers, BI, and AI systems. Shift-left here means:
- Making trust visible (quality signals and definitions travel with the data)
- Detecting anomalies quickly so you limit data downtime and tracing impact to make sure you prevent a high blast radius in the future
- Closing the loop so upstream teams improve, not just patch symptoms downstream
This is where many teams hit the “observability illusion.” Monitoring can feel like control, but without reusable data quality rules, lineage, and business context, you still spend days chasing symptoms.
Shift-left isn’t only about preventing issues. It’s also about responding with clarity when something breaks.
How to start shifting left without boiling the ocean
Shift-left requires focus and a pragmatic starting point:
- Pick one trust-critical outcome
A KPI, regulatory report, customer metric, or AI use case with real business exposure - Identify the top 10 expectations that define “good”
Start small: schema rules, completeness, freshness, reference values, and critical thresholds - Move those expectations upstream into two trust boundaries
- Add an enforcement point at ingestion
- Add a data quality gate in the pipeline before data is published for consumption
Then measure what changes:
- How often do the rules catch issues
- How quickly teams resolve issues (MTTR)
- How much data downtime did we avoid?
- Did the blast radius shrink?
- How many downstream incidents disappear over time
That measurement is what turns shift-left from a concept into an operating model.
Where Ataccama fits in this story
Shift-left succeeds when prevention and operations work together. That means enforcing trust boundaries across pipelines and transformations as well as running a closed loop when things change.
Ataccama’s approach brings those pieces into one platform: data quality controls, governance context, lineage impact, and now data observability to support a detect → triage → remediate loop.
What’s next in the series
If Part 1 is the “why,” Part 2 is the “how.” In Part 2, we’ll walk through a practical implementation playbook built around three components: Data contracts → data quality gates → feedback loops. You’ll see how these pieces fit together and how to evaluate approaches without adding more tool sprawl.